New wave of Android ransomware lurks behind FBI porn warning
Thousands of Android users are at risk of having their mobile devices and private content locked by a particularly ruthless ransomware that demands users to pay $500 to restore access to their smartphone, according to anti-malware provider Bitdefender.
A fresh strain of spam emails containing malicious .apk files has hit the inboxes of Android users in the last few days with more than 15,000 spam emails, including zipped files detected from servers located in Ukraine.
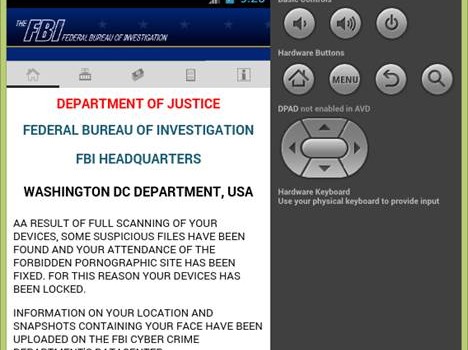
Posing as an Adobe Flash Player update, the malware is installed as an innocent video player. When the user begins to run it, a fake error message is displayed purported to be from the FBI.
After pressing “OK” to continue, users see an “FBI warning” and are unable to navigate away from the program. The device’s home screen then delivers an alarming fake message telling users they have broken the law by visiting pornographic websites. Hackers have also included screenshots of users’ purported browsing history in the malware to make the message more compelling and also claims to have screenshots of the victims’ faces and locations.
In order for users to restore access to their device, hackers demand $500. However, if users try to ‘independently unlock’ their devices, the demand triples to $1,500. Users are prompted to pay the fee by transferring money via Money Pak and PayPal My Cash.
Bitdefender has detected this threat as the ‘Android.Trojan.SLocker.DZ.’; one of the most prevalent Android ransomware families. According to Bitdefender’s internal telemetry, multiple versions of this malware family are available, bundled with spam messages originating from different .edu, .com, .org and .net domain servers.
Safety recommendations for users
Unfortunately, there is not much you can do when you fall victim to ransomware, even if this particular strain does not encrypt the files on the infected terminal. When a user is attacked by ransomware, the device’s home screen button and back functionalities are disabled. Turning the device on and off doesn’t help either because the malware continues running when the operating system boots.
In certain circumstances, Android users can reclaim control of their devices for instance if they have Android Data Bridge (ADB) enabled on their infected Android, as they can programmatically uninstall the ransomware application.
If supported by the mobile device, users can also start the terminal in Safe Boot which allows the user to load a minimal Android configuration which prevents the malware from running. This approach can buy you enough time to manually uninstall the malware..
Here is a useful list of recommendations for users to prevent falling victim to ransomware:
- Never install applications from untrusted sources. Android blocks the installation of applications outside the Play Store by default, but there are instances when users are forced to change the settings (i.e. when using third-party Android markets). If possible, leave this option in its default state.
- Regularly back up your data in the cloud or on an external drive.
- Use an anti-malware solution for your Android device and keep it constantly updated and able to perform active scanning.
- Follow good internet practices; avoid questionable websites, links or attachments in emails from uncertain sources.
- Use a filter to reduce the number of infected spam emails that reach your inbox.
This article is based on the technical information provided courtesy of Bitdefender Senior Antispam Researcher Adrian MIRON, Malware Researchers Alin BARBATEI and Vlad ILIE.